AI in Cybersecurity for Resilient, Proactive Enterprise Defense
Deploy ai in cybersecurity built on 19+ years of deep engineering expertise. Our team integrates advanced machine learning and automated response architectures to protect business continuity and defend high-stakes digital assets against evolving threats.
19+ years of product and security engineering expertise
AI-first proactive threat intelligence
Flexible engagement and dedicated security squads
Trusted by global brands to secure mission-critical assets







4.5  based on 1200+ reviews
based on 1200+ reviews

Strategic Defense of Intelligent Defense
To protect complex digital ecosystems, leaders must move beyond manual monitoring. Effective ai in cybersecurity integrates predictive modeling, behavioral analysis, and rapid remediation. This technology ensures data integrity and operational resilience necessary for sustainable growth in an era of automated attacks.
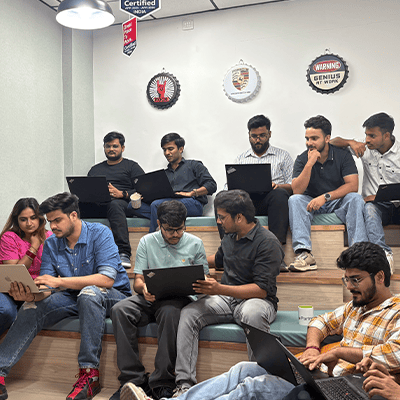
When you partner with our team, you gain access to structured defense, enhanced monitoring, and high-performance ai cybersecurity solutions. We build custom security frameworks that balance accessibility with zero-trust protocols, ensuring your infrastructure remains secure as it scales.
Why
WildnetEdge ?
When you choose to work with us, we align technical defense with your business outcomes through structured planning and scalable architecture. We have secured 200+ enterprise solutions with a disciplined engineering team that understands the intersection of strategy and execution.
Whether you need a specific pilot or a complete overhaul, our use of ai in cybersecurity supports secure, high-speed growth. We enable faster decision cycles and reduce dependency on manual monitoring through intelligent automation.
AI in Cybersecurity: Our End-to-End Defense Process
When we implement ai in cybersecurity, we follow a structured, outcome-focused lifecycle designed to balance protection, usability, and performance. Our process ensures every technical decision supports long-term scalability.
METHOD. MASTERY. MEASURABLE IMPACT.

Industry-Focused Enterprise Solutions
At Wildnet Edge, we build frameworks that fit your specific industry model. We build tools tailored to your operational realities and compliance needs.

Highlights:
Frequently Asked Questions
What is eCommerce development, and how is it different from using a platform like Shopify or Wix?
eCommerce development refers to building a custom or semi-custom digital store tailored to your business model, product types, and growth goals. Unlike platforms like Shopify or Wix, custom eCommerce development gives you complete control over user experience, backend logic, integrations, and scalability, no templates, no platform limits, just a solution built for your needs.
Why choose WildnetEdge for eCommerce website development?
Because we go beyond design, we build revenue-ready digital storefronts that integrate with your CRM, ERP, and supply chain. With 19+ years of full-stack experience and expertise in enterprise eCommerce development, we don’t just launch websites, we launch growth platforms. Plus, you get full source code ownership, no lock-ins, and a team that speaks both business and tech.
Do you build both B2C and B2B eCommerce solutions?
Yes. We’ve delivered high-performance eCommerce platforms across B2C, B2B, and hybrid models. Whether you need a consumer-friendly storefront or a feature-rich B2B portal with bulk pricing, custom logins, and approval workflows, we’ve done it, and we can tailor it to your industry.
How long does a custom eCommerce development project take?
Timelines vary based on complexity. A basic store can launch in 6–8 weeks, while enterprise-grade eCommerce platforms with multiple integrations may take 3–6 months. We work in agile sprints with regular releases, so you can go live with core features faster and scale functionality as needed.
Can you integrate our existing tools and backend systems?
Absolutely. We specialize in building custom eCommerce solutions that integrate with your CRM, ERP, payment gateways, shipping APIs, marketing tools, and more. We’ll make sure your operations stay streamlined and connected.
Will we own the source code and IP?
Yes. All deliverables, including source code, documentation, and IP, are 100% yours after completion. We believe in full transparency and long-term trust, with no vendor lock-in.
 sales@wildnetedge.com
sales@wildnetedge.com +1 (212) 901 8616
+1 (212) 901 8616 +1 (437) 225-7733
+1 (437) 225-7733





 ChatGPT Development & Enablement
ChatGPT Development & Enablement Hire AI & ChatGPT Experts
Hire AI & ChatGPT Experts ChatGPT Apps by Industry
ChatGPT Apps by Industry ChatGPT Blog
ChatGPT Blog ChatGPT Case study
ChatGPT Case study AI Development Services
AI Development Services Industry AI Solutions
Industry AI Solutions AI Consulting & Research
AI Consulting & Research Automation & Intelligence
Automation & Intelligence